AI-generated image. No copyright claimed or implied.
Incident at a Glance
97M
monthly downloads
< 1 hr
before detection
Total
credential scope
0
security tools caught it
On March 24, 2026, a poisoned version of LiteLLM was quietly pushed to PyPI. LiteLLM is one of the most widely used AI infrastructure libraries in the world, 97 million downloads a month. Most developers who use it never think twice about it.
Version 1.82.8 contained a malicious .pth file that ran automatically on every Python process startup, no import required. It harvested SSH keys, cloud credentials, Kubernetes configs, database passwords, and API keys, then sent everything to an attacker-controlled server. It also tried to move laterally into Kubernetes clusters and install a persistent backdoor.
The package stayed live for less than an hour. It wasn't caught by a scanner or any security tool. It was caught because the malware had a bug, a fork bomb that crashed the victim's machine. Without that bug, this could have run silently across thousands of AI development environments for weeks.
“The attacker made a mistake. That is not a defence strategy.”
The blast radius was larger than LiteLLM's own download numbers suggest. Projects that depended on LiteLLM, including DSPy, OpenClaw, and Hermes, would have pulled in the compromised package automatically through transitive dependencies, with no direct action needed from the developer. These are foundational libraries in the AI development ecosystem. A clean exfiltration would have compromised entire organisations through a single developer machine.
If You Use LiteLLM: Check Right Now
Run this to check your installed version:
pip show litellmIf the version shown is 1.82.7 or 1.82.8, treat all credentials on that machine as compromised and act immediately:
# 1. Uninstall the compromised version
pip uninstall litellm
# 2. Pin to a safe version
pip install "litellm<=1.82.6"
# 3. Purge pip cache
pip cache purgeThen rotate all credentials immediately, SSH keys, cloud provider tokens (AWS, GCP, Azure), API keys, database passwords, git credentials, and anything in .env files on that machine.
Also check for persistence. The malware installed a backdoor at ~/.config/sysmon/sysmon.py. If that file exists, remove it. If you're running Kubernetes, audit the kube-system namespace for any pods you don't recognise.
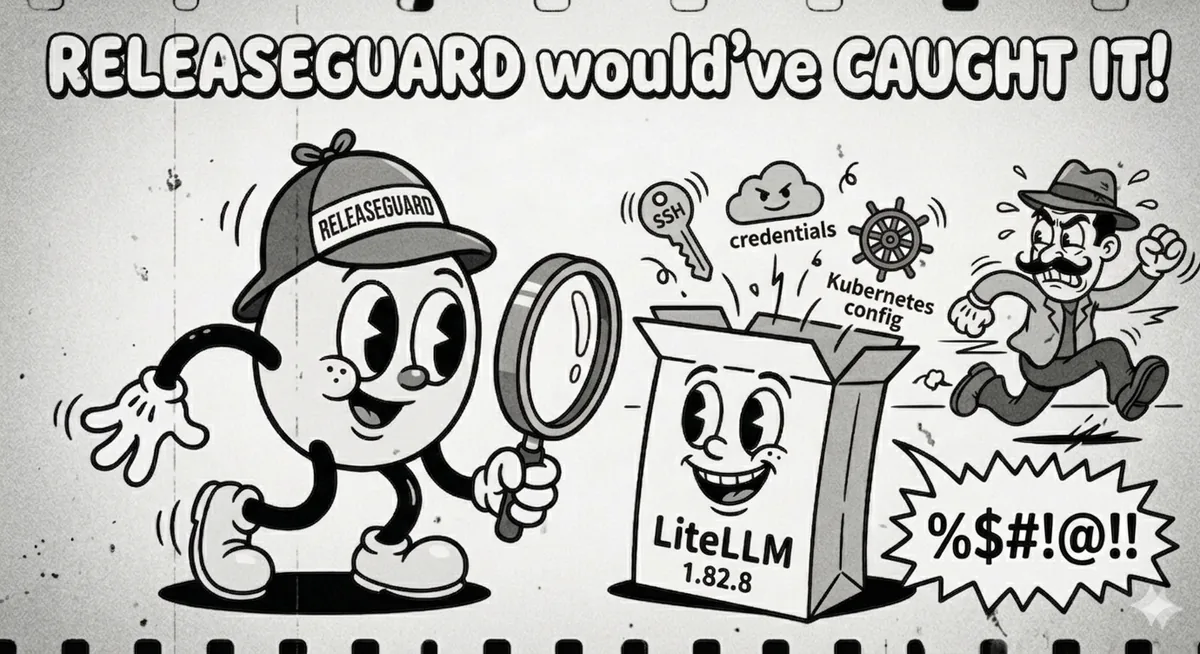
Why Helixar Built ReleaseGuard
This is exactly the attack vector Helixar has been building against since the company's founding. The premise of ReleaseGuard, our open source artifact scanner, is simple: you can't manually review every release in your dependency tree, and you can't rely on package registries to catch malicious uploads before they reach users. Automated artifact scanning at release time is the only answer.
ReleaseGuard scans software artifacts and generates SBOMs, flagging anomalies like unexpected files, suspicious encodings, and credential-harvesting patterns, the exact class of payload in litellm_init.pth. It's free, MIT-licensed, and available on GitHub and the GitHub Marketplace.
Open Source
ReleaseGuard on GitHub
Artifact scanning, SBOM generation, and release attestation. Free, MIT-licensed, available on GitHub Marketplace. No account required for core functionality.
What Made This Attack Dangerous
The LiteLLM incident isn't an anomaly. It's a preview. As AI infrastructure gets more modular, MCP plugins, agent frameworks, LLM routing layers, the dependency surface expands with it. Every new package is a potential vector. Three things made this one particularly bad:
- Silent execution via .pth files. A
.pthfile runs on every Python process startup, not just when the package is imported. Standard import scanning misses it entirely. - Direct PyPI upload, no GitHub trail. The package bypassed the project's GitHub release process completely, no tag, no release notes, no diff for maintainers to spot.
- Total credential scope. SSH keys, cloud tokens, Kubernetes configs, git credentials, shell history, crypto wallets,
.envfiles. One compromised developer machine could have taken down an entire organisation.
“The question is not whether this will happen again. It is whether you will know when it does.”
The Structural Problem
PyPI runs on trust. Maintainers upload packages, users install them, and almost nothing automated checks what's in between. PyPI doesn't scan uploads for malicious payloads. GitHub release pipelines are optional. Code signing is rare. SBOMs are rarer.
The LiteLLM attack exploited every one of these gaps. The only reason it was caught in under an hour was a bug in the malware itself, not any defensive measure in the ecosystem.
One compromised package. 97 million monthly downloads. Thousands of downstream projects. The cost of poisoning one package is trivial compared to the cost of auditing every package in every dependency tree. Automated scanning is the only way to close this gap at scale.
ReleaseGuard is designed to close this gap, by scanning artifacts at release time, generating a complete SBOM, and flagging anomalies before distribution. It doesn't replace code review. It catches what code review can't, especially in transitive dependencies nobody is manually auditing.
A Word from the Helixar CEO
“We have been saying this was coming. The LiteLLM attack is not a surprise, it's a confirmation. When we founded Helixar, we predicted that AI infrastructure supply chains would become one of the highest-value targets in the threat landscape. We built ReleaseGuard because we saw this exact vector materialising, and we've predicted many more like it.
I want everyone building with open source AI tooling to adopt ReleaseGuard and help improve it. Automated artifact scanning should be a baseline expectation for every software release, not an optional extra. That's the standard we're pushing toward.
The threat landscape is moving faster than any single team can keep up with alone. We're a bootstrapped company racing against agentic threats that the entire industry is underprepared for, and we're looking for the people who want to help us win that race. If you're a builder who wants to work on hard security problems, a researcher who sees where this is heading, or a VC who wants to back a team that called this early, we want to talk.”
CEO, Helixar.ai
About Helixar
Helixar is an AI-native cybersecurity company building endpoint and API security for the agentic AI era. Its products include the Vigil endpoint agent, the Shield/ATP inbound API inspection layer, and FishBowl, the first OS-native sandbox purpose-built for AI agents. Helixar Labs maintains a suite of open source security tools including ReleaseGuard, Sentinel, and Unpinched.
Helixar is based in Auckland, New Zealand, and is currently in free pilots.
References
- BerriAI. (2026). LiteLLM GitHub Repository. GitHub. github.com/BerriAI/litellm
- Python Packaging Authority. (2026). LiteLLM on PyPI. PyPI. pypi.org/project/litellm
- OWASP. (2023). OWASP Top 10 CI/CD Security Risks. Open Web Application Security Project. owasp.org
- CISA. (2024). Defending Against Software Supply Chain Attacks. Cybersecurity and Infrastructure Security Agency. cisa.gov
- NIST. (2022). Secure Software Development Framework (SSDF), SP 800-218. National Institute of Standards and Technology. csrc.nist.gov
- The Linux Foundation. (2023). SLSA: Supply-chain Levels for Software Artifacts. slsa.dev
- Sonatype. (2025). State of the Software Supply Chain Report. sonatype.com
- The Hacker News. (2026). Malicious PyPI Package Targets LiteLLM Users with Credential-Harvesting Malware. thehackernews.com