At a Glance
3
open-source tools
MIT
licensed, fully auditable
Free
on GitHub Marketplace
0
credentials required for core scans
Helixar Labs has published three open-source security tools in Q1 2026, each targeting a distinct gap in the current security stack: artifact-level policy enforcement, MCP server configuration hardening, and live MCP traffic analysis. All three are MIT-licensed, available on GitHub Marketplace at no cost, and require no Helixar account to run core functionality.
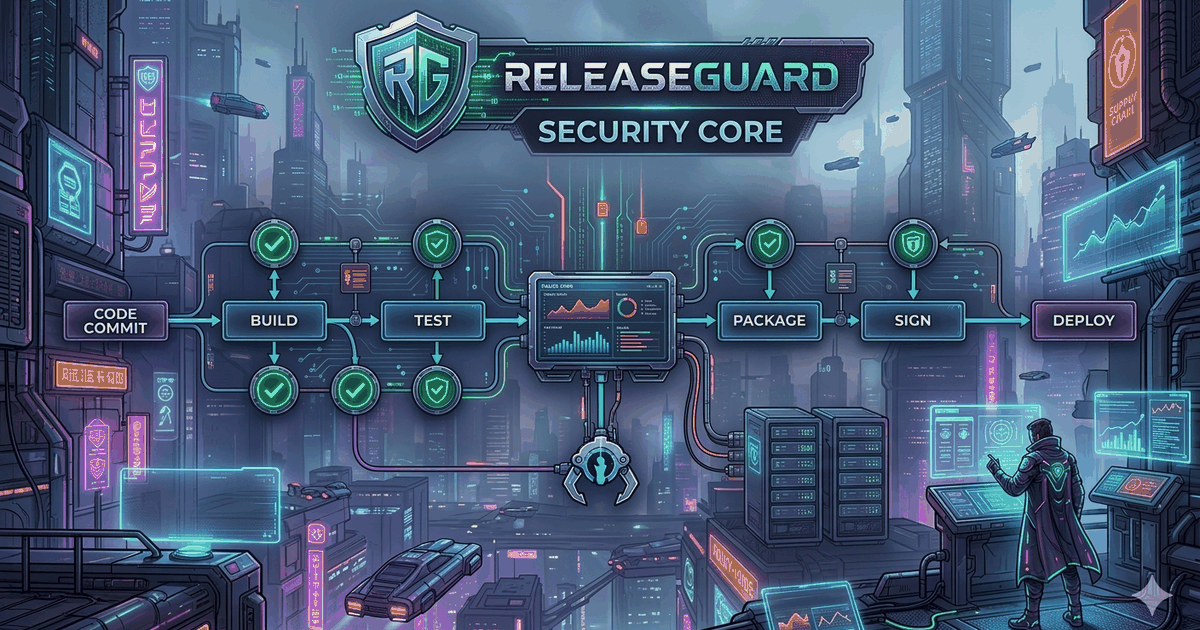
ReleaseGuard: Artifact Policy Engine
Supply chain security tooling has historically focused on source code, dependencies, and container images. The SolarWinds compromise drew attention to build pipelines; the XZ Utils backdoor drew attention to the maintainer layer. The final distributable — the exact artifact that reaches users — has received comparatively little scrutiny.
ReleaseGuard scans dist/ and release/ outputs for common post-build leakage: embedded API keys and tokens, accidentally shipped source maps, debug symbols in release binaries, .env files baked into builds, and unsigned executables. It then applies hardening transforms, generates a full SBOM in CycloneDX or SPDX format, and produces a signed, attested artifact with an evidence bundle.
Source and dependency scanning catches what goes into a build. Artifact scanning catches what comes out. ReleaseGuard addresses the gap between them.
A single command — releaseguard check ./dist — produces a policy result with no configuration and no external network calls. SBOM generation covers all major ecosystems (Node.js, Python, Go, Rust, Java, .NET, Ruby, PHP, container, and system packages). Signing is available via keyless Sigstore for CI environments with OIDC tokens, or via local key material. Provenance attestations follow the SLSA framework to level 2 by default, with level 3 available in the cloud tier.
“Source scanning tells you what went into the build. Artifact scanning tells you what your users are actually receiving. Those are not always the same thing.”
The ReleaseGuard GitHub Action wraps the full pipeline — check, fix, SBOM, sign, attest — into a single workflow step. Policy is configurable via YAML, with support for Open Policy Agent Rego rules and OCI registry bundle loading. Reports export in CLI, JSON, SARIF, Markdown, and HTML. Source is MIT-licensed at github.com/Helixar-AI/ReleaseGuard.
ReleaseGuard on ClawHub
ReleaseGuard is also published as a skill on ClawHub, the marketplace for OpenClaw agents. Once installed, OpenClaw agents can invoke ReleaseGuard through natural language — scanning artifacts, generating SBOMs, or running the full hardening pipeline — without manual CLI configuration.
ReleaseGuard via OpenClaw
Natural Language
Invoke scans, fixes, and signing through conversation — no CLI flags required
Auto-Install
Skill installs the binary via Homebrew automatically
Full Pipeline
check → fix → sbom → sign → attest → verify, all conversationally
Each command in the skill documentation specifies whether external network calls are made, which service is contacted, and whether credentials are required. The default path — check, fix, sbom — is fully offline. Signing and cloud features are opt-in and explicitly disclosed.
Sentinel and the MCP Security Checklist
The Model Context Protocol (MCP), introduced by Anthropic in November 2024, has become the standard integration layer between AI agents and external tools, APIs, and data sources. Adoption has been rapid, but security practices have not kept pace. The protocol specification defines transport and schema; it does not define authentication, input validation, or output sanitisation requirements. Those are left to individual implementers.
MCP servers run with user-level permissions and can access any resource the host application can reach. A misconfigured server is a privilege escalation path into the full scope of the user's environment.
Helixar Labs has published two tools in response. The MCP Security Checklist covers pre-deployment hardening: authentication, input validation, tool schema constraints, output filtering, transport security, and audit logging. Each item maps to a concrete attack scenario and is designed to serve as a deployment gate, not a reference document.
Sentinel covers runtime risk. Available free on GitHub Marketplace, it scans live MCP traffic, detects anomalous tool invocation patterns, flags prompt injection attempts embedded in tool outputs, and surfaces unexpected permission escalation chains. Together, the checklist and Sentinel cover both the configuration and runtime layers.
| Tool | When | What It Catches |
|---|---|---|
ReleaseGuard Artifact Layer | Pre-distribution — scans the final build artifact before it ships | Embedded secrets, source maps, debug symbols, unsigned binaries, missing SBOMs |
MCP Security Checklist Configuration Layer | Pre-deployment — audits MCP server configuration against security requirements | Missing auth, unsafe tool schemas, absent input validation, over-privileged access |
Sentinel Runtime Layer | Live — monitors MCP traffic for anomalous patterns and injection attempts | Prompt injection in tool outputs, anomalous invocation chains, unexpected escalation |
Why Open Source
Security tooling that cannot be audited asks users to trust vendor claims. In supply chain security specifically — where the problem is trusting the provenance of what you run — a closed-source scanner is structurally inconsistent with the trust model it is meant to enforce. Open source does not guarantee trustworthiness, but it enables independent verification: public code review, reproducible builds, and community scrutiny at a scale no internal review process can match.
There is also a practical consideration. The gaps these tools address — artifact-level leakage, MCP misconfiguration, agent runtime anomalies — are not gaps a single team can fully characterise from its own deployment data. Open-source projects accumulate real operational experience through issue reports and contributions that accelerate coverage beyond what any proprietary product can achieve independently.
Standards Context: SLSA, SBOM, and Sigstore
ReleaseGuard is built around three standards with growing compliance relevance:
- SLSA — a four-level provenance assurance framework from Google and the OpenSSF. ReleaseGuard produces SLSA level 2 attestations by default; level 3 is available in the cloud tier.
- SBOM — mandated by US Executive Order 14028 for federal software procurement and increasingly required in enterprise contracts. ReleaseGuard generates SBOMs in CycloneDX and SPDX with optional CVE enrichment via OSV.dev.
- Sigstore — Linux Foundation keyless signing infrastructure using Fulcio CA and the Rekor transparency log. Sigstore eliminates long-lived key material from the signing workflow. ReleaseGuard's default signing mode uses Sigstore directly.
Availability
All three tools are available now at no cost:
- ReleaseGuard — installable via Homebrew, available as a GitHub Action, and published as an OpenClaw skill on ClawHub
- Sentinel — available as a GitHub Action on GitHub Marketplace
- MCP Security Checklist — publicly maintained on GitHub
None require an account, cloud token, or commercial relationship to run core functionality. The US Executive Order on Cybersecurity, the EU Cyber Resilience Act, and NTIA minimum SBOM standards are creating compliance requirements across the software supply chain. Teams that adopt these practices proactively will be better positioned when procurement or incident response demands them.
References
- Helixar AI. (2026). ReleaseGuard: Artifact Policy Engine. GitHub. github.com/Helixar-AI/ReleaseGuard
- Helixar AI. (2026). Artifact Policy Engine — GitHub Marketplace. GitHub. github.com/marketplace/actions/artifact-policy-engine
- Helixar AI. (2026). Sentinel MCP Security Scanner — GitHub Marketplace. GitHub. github.com/marketplace/actions/sentinel-mcp-security-scanner
- OpenSSF & Google. (2023). SLSA: Supply-chain Levels for Software Artifacts. Open Source Security Foundation. slsa.dev
- Linux Foundation / Sigstore. (2024). Sigstore: Keyless Signing for Open Source. Sigstore. sigstore.dev
- CISA. (2023). Software Bill of Materials (SBOM). Cybersecurity and Infrastructure Security Agency. cisa.gov/sbom
- CycloneDX. (2024). CycloneDX SBOM Standard. OWASP. cyclonedx.org
- SPDX. (2024). SPDX: Software Package Data Exchange. Linux Foundation. spdx.dev
- OpenSSF. (2024). OSV: Open Source Vulnerability Database. Google / OpenSSF. osv.dev
- Anthropic. (2024). Model Context Protocol: Open Standard for AI Tool Integration. Anthropic. modelcontextprotocol.io
- OpenClaw. (2025). OpenClaw: Open-Source AI Agent Platform. GitHub. github.com/openclaw/openclaw
- OpenSSF. (2024). XZ Utils Backdoor Explained. Open Source Security Foundation. openssf.org
- OWASP. (2023). OWASP Top 10 for LLM Applications. Open Web Application Security Project. owasp.org
- Executive Office of the President. (2021). Executive Order 14028: Improving the Nation's Cybersecurity. The White House. whitehouse.gov