AI-generated image. No copyright claimed or implied.
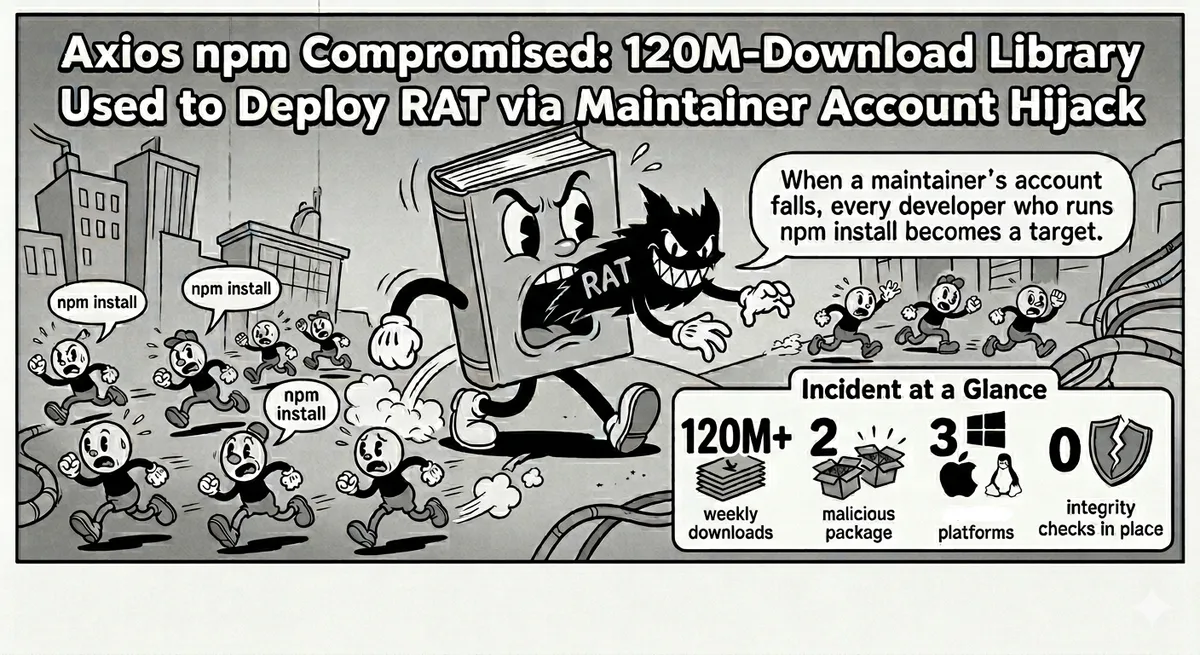
Incident at a Glance
100M+
weekly npm downloads
2
malicious versions published
3
platforms targeted
0
integrity checks in place
On March 31, 2026, attackers hijacked the npm account of jasonsaayman, the lead maintainer of axios, and published two malicious package versions containing a cross-platform remote access trojan. Axios has over 100 million weekly downloads. It is one of the most widely depended-upon JavaScript libraries ever written.
This is not a theoretical supply chain risk. This is a confirmed, active incident targeting the JavaScript ecosystem at its widest point. If you or your CI pipeline ran npm install axios on March 31 before the packages were removed, you need to act now.
“One compromised maintainer account. One hundred million potential install targets. No verification step in between.”
Check Your Environment Right Now
Check whether you installed a malicious version:
npm list axiosThe two compromised versions are axios@1.14.1 and axios@0.30.4. If either appears in your output, treat the machine as compromised. Rotate all secrets, tokens, and credentials accessible from it.
Update to a clean version immediately:
# Remove and reinstall a safe version
npm uninstall axios
npm install axios@1.7.9
# Clear npm cache
npm cache clean --forceStandard node_modules inspection will not reveal the compromise after the fact , the malware self-deletes after execution. Check your system logs for outbound connections to sfrclak[.]com (IP: 142.11.206[.]73). Any hit on that domain means the RAT executed.
Indicators of Compromise
These are the technical indicators published by researchers. Use them for log review, EDR queries, and network blocking:
IOCs
Malicious packages
axios@1.14.1axios@0.30.4plain-crypto-js@4.2.1Package hashes (SHA-1)
axios@1.14.1 , 2553649f2322049666871cea80a5d0d6adc700caaxios@0.30.4 , d6f3f62fd3b9f5432f5782b62d8cfd5247d5ee71plain-crypto-js@4.2.1 , 07d889e2dadce6f3910dcbc253317d28ca61c766C2 infrastructure
sfrclak[.]com:8000142.11.206[.]73Attacker accounts
jasonsaayman (legitimate account, hijacked)nrwise (attacker-created, published plain-crypto-js)How the Attack Worked
The attack unfolded in three hours. It is methodical, and every step exploited a gap that the npm ecosystem has no automated control for.
First, at 23:59 UTC on March 30, the attacker account nrwise published a new package called plain-crypto-js@4.2.1 to npm. This package had never existed before. It contained a postinstall hook , a script that runs automatically when the package is installed , that dropped a platform-specific RAT payload and called home to sfrclak[.]com:8000.
Then the attackers used the compromised jasonsaayman account to publish two new axios versions , 1.14.1 at 00:21 UTC and 0.30.4 at 01:00 UTC , each adding plain-crypto-js as a dependency. Since axios is a direct dependency for tens of millions of projects, any developer or CI pipeline that ran npm install in that two-hour window pulled the malicious package automatically with no warning and no prompt.
- macOS: A binary disguised as an Apple system daemon was dropped to
/Library/Caches/com.apple.act.mond, designed to blend in with legitimate Apple cache processes. - Windows: A hidden VBScript launched a PowerShell dropper, writing the payload to
%PROGRAMDATA%\wt.exe. - Linux: A Python script was written to
/tmp/ld.pyand executed.
After executing, the dropper self-deleted to hinder forensic analysis. A clean install of the malicious version leaves no trace in node_modules.
Timeline
| Time (UTC) | Event |
|---|---|
| Mar 30, 23:59 | Attacker account nrwise publishes plain-crypto-js@4.2.1 to npm with RAT postinstall hook. |
| Mar 31, 00:21 | Compromised jasonsaayman account publishes axios@1.14.1 with plain-crypto-js as a dependency. |
| Mar 31, 01:00 | Second malicious release: axios@0.30.4 published by the same compromised account. |
| Mar 31, ~03:xx | Incident discovered. Both axios versions and plain-crypto-js removed from npm by the registry. |
This Is Not New. The Scale Is.
Maintainer account takeovers and poisoned dependencies are not a new class of attack. But the targets are getting bigger. The axios compromise joins a long line of high-impact supply chain incidents, each one exploiting the same structural gap: package registries accept uploads from any authenticated account, and nobody automatically verifies that the package contents are consistent with the project's known behaviour.
Notable Supply Chain Incidents
event-stream (2018, npm)
A malicious contributor gained maintainer rights through apparent goodwill, then injected code targeting the Copay Bitcoin wallet. Downloaded 8 million times before discovery. The first major demonstration that social trust in open source is exploitable at scale.
SolarWinds Orion (2020)
Nation-state attackers (APT29/Cozy Bear) compromised the SolarWinds build pipeline and inserted a backdoor into signed Orion software updates. Reached 18,000 organisations including US government agencies. The canonical case for why signed releases alone are insufficient.
node-ipc (2022, npm)
The package maintainer intentionally added destructive payload to a widely used utility, targeting users in Russia and Belarus. Demonstrated that the threat is not just external attackers , maintainer intent cannot be assumed.
XZ Utils (2024)
A patient two-year social engineering operation saw a malicious contributor gain maintainer trust on a critical Linux compression library and insert an SSH backdoor. Discovered only because of an anomalous 500ms latency noticed by a Microsoft engineer. The most sophisticated open source supply chain attack ever documented.
A poisoned version of LiteLLM, 97 million monthly downloads, was pushed to PyPI via a compromised account. A credential-harvesting payload ran on every Python process startup via a .pth file , no import required. Caught only because the malware had a bug that crashed victim machines. One week before the axios incident.
“The LiteLLM attack and the axios attack happened one week apart. Different registries. Same playbook: account compromise, malicious dependency, postinstall hook, self-deleting payload. The ecosystem has not learned from this pattern because there is no automated mechanism to detect it.”
Why npm Cannot Catch This
When jasonsaayman's account published axios@1.14.1, it was a cryptographically valid, authenticated publish by the account that owns the package. From npm's perspective, there was nothing anomalous about it.
That is the structural problem. npm authenticates the publisher. It does not verify that what was published is consistent with what that publisher has always published. It does not check whether a dependency that has never appeared in axios was just added. It does not scan postinstall scripts for network callbacks to unknown infrastructure. It trusts the token, not the content.
npm (and PyPI, and most other registries) operate on identity-based trust: if you have the right credentials, you can publish anything. Content-based trust , scanning what was published against what you'd expect , requires a separate layer that almost no project has. That layer is exactly what ReleaseGuard provides.
How Helixar ReleaseGuard Catches This Class of Attack
Helixar ReleaseGuard is an open-source artifact policy engine that scans software releases before they are distributed and flags anomalies that indicate supply chain compromise. It is available free on GitHub and the GitHub Marketplace, requires no account for core functionality, and takes under five minutes to integrate into a CI pipeline.
The axios attack had three detectable signals , all of which ReleaseGuard would have flagged at publish time:
What ReleaseGuard Detects
- Unexpected new dependency.
plain-crypto-jswas never in any prior axios release. ReleaseGuard diffs the SBOM of every release against the previous one and raises an alert when a previously unseen package is added , especially from an account with no prior history in the project's dependency graph. - Postinstall script with network callback. ReleaseGuard scans lifecycle scripts (postinstall, preinstall, install) for outbound network calls, shell execution chains, and file writes to system directories. The
setup.jspayload inplain-crypto-jswould have matched multiple heuristics. - Platform-specific binary drop. Writing binaries to
/Library/Caches/,%PROGRAMDATA%, or/tmp/from an npm postinstall hook is high-confidence malicious behaviour. ReleaseGuard's artifact policy rules flag this pattern explicitly.
Critically, ReleaseGuard can be run on the consuming side too, not just by the publisher. If your CI pipeline scans the npm tarball of any new dependency version before it is installed, you would have blocked plain-crypto-js@4.2.1 before it ever executed on your systems. This is the defence-in-depth posture that the industry needs to normalise.
Open Source
ReleaseGuard by Helixar Labs
Artifact scanning, SBOM generation, and release attestation for npm, PyPI, and more. Free, MIT-licensed. Available on GitHub and the GitHub Marketplace. Integrates with your existing CI in minutes.
What Every Team Should Do Before the Next Incident
The axios attack and the LiteLLM attack one week earlier make the same point: your CI pipeline is pulling packages from registries that do not verify content, and you are probably not verifying it either. Here is a baseline every team should have in place.
Supply Chain Security Baseline
- Lock your lockfiles. Commit
package-lock.json(oryarn.lock/pnpm-lock.yaml) and enforcenpm ciin CI, nevernpm install. This prevents unintended minor/patch version bumps from pulling in a compromised release. - Use npm audit in every build. It won't catch zero-days, but it catches known malicious packages once they are flagged. Fail the build on high-severity findings.
- Scan tarballs with ReleaseGuard. Add artifact scanning to your CI pipeline. Scan new dependency versions before they install. Flag unexpected new transitive dependencies. This catches what
npm auditcannot , unknown-malicious packages that have not yet been reported. - Enable MFA on all package registry accounts. The axios attack was a maintainer account hijack. MFA on the npm account would have prevented the malicious publish. Every organisation with packages on npm, PyPI, or any other registry should enforce this today.
- Require package provenance attestation. npm now supports provenance statements that link a published package to its source repository and CI build. Prefer packages published with provenance, and require it for packages you maintain.
- Subscribe to security advisories. GitHub's Dependabot and npm's advisory feed notify you when packages you depend on receive a security advisory. This shortens your detection window from “when a developer notices something strange” to minutes.
The Broader Picture: Developer Tools Under Attack
Axios is not an AI library. It is a general-purpose HTTP client used across the entire JavaScript ecosystem. The targeting logic here is straightforward: attack the tool that every developer uses, not the tool that some developers use.
But the pattern is accelerating specifically in the AI development toolchain. In the last month alone we have documented the LiteLLM PyPI attack targeting AI developers, the Qihoo 360 SSL key exposure in a public AI product installer, and now the axios compromise. The tools used to build AI applications are being targeted deliberately, because the developers of AI applications are high-value targets: they have access to cloud infrastructure, LLM API keys, proprietary datasets, and production deployment credentials.
If you are building in the AI space and have not thought carefully about your supply chain posture, the attackers have already thought about it for you.
- LLM API keys (OpenAI, Anthropic, Google) , high unit cost, immediate resale value
- Cloud infrastructure credentials with GPU instance access
- Proprietary training data and fine-tuned model weights
- Production deployment secrets across Kubernetes, AWS, GCP, Azure
- Customer data pipelines with PII and enterprise data
References
- Aikido Security. (2026, March 31). Axios npm Compromised: Maintainer Hijacked, RAT Deployed. aikido.dev
- npm. (2026). axios package on npm registry. npmjs.com/package/axios
- CISA & NSA. (2023). ESF Recommended Practices Guide: Software Supply Chain for Developers. cisa.gov
- OWASP. (2023). OWASP Top 10 CI/CD Security Risks. owasp.org
- NIST. (2022). Secure Software Development Framework (SSDF) SP 800-218. csrc.nist.gov
- Sonatype. (2025). 9th Annual State of the Software Supply Chain Report. sonatype.com
- OpenSSF. (2024). The XZ Utils Backdoor: A Timeline and Technical Analysis. openssf.org
- npm. (2023). Generating provenance statements. docs.npmjs.com
- Helixar Research Team. (2026, March 25). LiteLLM Supply Chain Attack: Malware Found in 97-Million-Download AI Library. helixar.ai/press/litellm-pypi-supply-chain-releaseguard/
- Helixar Research Team. (2026, March 16). Qihoo 360 Shipped a Private SSL Key Inside Their Installer. helixar.ai/press/qihoo-360-ssl-key-installer-releaseguard/